Even when encryption correctly hides a messages content and it cannot be tampered with at rest or in transit a messages length is a form of metadata that can still leak sensitive information about the message. Asymmetric encryption uses two keys for encryption and decryption.
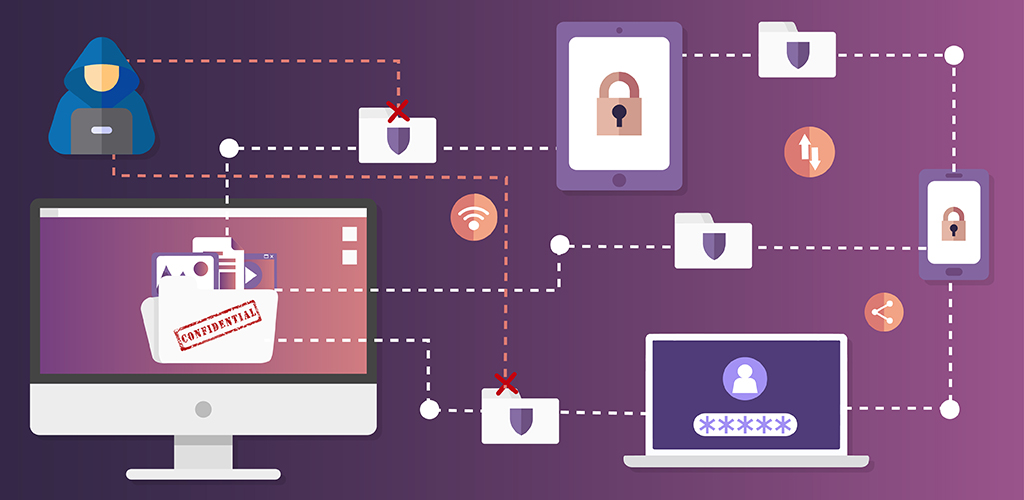
Securing Confidential Files Information Services University Of Regina
4 Encryption Tools For Windows 10 OS 1 WINZIP.
Encrypting files for confidentiality. For example the well-known CRIME and BREACH attacks against HTTPS were side-channel attacks that relied on information leakage via the length of encrypted content. The WINZIP tool is used to encrypt the data on the computers like PC laptop and server into a compress. BitLocker is deployed for OneDrive for Business and SharePoint Online across the service.
Encrypting a file encodes its contents so that the file cannot be read until it is decrypted. Heres how theyre different. Sending encrypted files with macOS.
Folder Lock is an impressive security app that provides the highest standard file locking. EFS is available in all versions of Windows except the home versions see Supported operating systems below. BitLocker disk-level encryption and per-file encryption of customer content.
We can apply both concepts to data in transit or at rest. Integrity comes from hashing the file so any change no matter how minute can be instantly detected. Encryption at rest includes two components.
Encryption is the heart of Smartcrypt. Recommended security parameters for file encryption on disk. In the service and as a customer control.
The encrypting file system uses encryption to encrypt files and folders to ensure confidentiality. This is a great tool. You dont have to configure anything.
You must never send personal sensitive or confidential information to a non-secure email address unless it is encrypted. For Outlook 2019 and Outlook 2016 In an email message choose Options select Permissions. Confidentiality is the concept of ensuring that data is not made available or disclosed to unauthorized people.
However this option does not work for users outside of my company. The University requires that a ny device that holds sensitive or confidential information is encrypted. Confidentiality comes when the file is encrypted in such a way that only authorized users have access to the key.
The encrypted option is an additional feature providing client-side encryption to password protect files as they speed across the net. See Encrypting your device below for further advice. The Encrypting File System EFS on Microsoft Windows is a feature introduced in version 30 of NTFS that provides filesystem-level encryptionThe technology enables files to be transparently encrypted to protect confidential data from attackers with physical access to the computer.
A cipher is a mathematical algorithm used to scramble data. Under Options tab - Permission section - Permission I click the option of confidential to send an encrypted email to users inside of my company. If you are using macOS you can send encrypted files by following these steps.
Protecting confidential data We offer guidance and support to help you protect your confidential data whether its files that you need to share securely or a device that requires encryption. Create a new folder and drag all files you want to encrypt into this folder. Sending sensitive information to non-secure email addresses including patients Encryption is an additional security tool which means users can communicate securely to any type of email account.
Encryption can be used to provide both confidentiality and integrity. Please note however that the attachment size is usually limited to 25 MB for e-mail providers. How do I change the setting for all or specific users to have access to send encrypted emails to external users as well.
Confidentially is achieved through encryption. A private key which is not shared decrypts the data. A public key which is shared among users encrypts the data.
In an email message choose Options select Encrypt and pick Encrypt with SMIME option from the drop down Youll see an Encrypt with SMIME if you have an SMIME certificate installed on your computer. Encrypt and Password-protect all your confidential files and folders and maintain your privacy. My goal is to optimize the key usage before there is a need to re-generate the key or the initialization vector IV.
In the service encryption is used in Microsoft 365 by default. Crypto-Expert tool is a far more powerful secure and reliable data security tool than the other. Encryption protects data by making it unreadable until it is decrypted or unscrambled using the correct cipher and key.
Encryption is the process by which information is encoded so that only an authorized recipient can decode and consume the information. Symmetric encryption uses a single password to encrypt and decrypt data. This is the optimal recommended usage for the specified GCM parameters when encrypting files of different size on disk.
Another strength here is the wide range of supported devices. Decrypting removes the encry. So you can encrypt your important files and backup real-time files as well.
Depending on your configuration the file or folder that is encrypted may show a lock. Its simple and secure. It allows you to create password-protected folders and drives.
Asymmetric encryption can be used and well discuss them later. You can now also send the encrypted files by e-mail. Encryption converts data such as a document or spreadsheet into an unintelligible scrambled format to protect the confidentiality of the data.
Microsoft 365 uses encryption in two ways.